We already done OpenVPN setup on pFSense and now we are able to connect to VPN, but we are still not able to access to the LAN resources across VPN connection.
Before we proceed with the LAB, here is the configuration of my LAB
Host: Windows Server 2016 STD Eval – 10.20.20.2/16
Firewall/VPN: pFSense 2.3.4 – LAN Interface: 10.20.20.1/16
WAN Interface: Static IP
OpenVPN Interface for clients: 192.168.1.0/28
Machine that will be connecting to the OpenVPN is Windows Server 2012 R2 STD Eval – Random local IP outside of 10.20.xx.xx or 192.169.xx.xx range.
You can follow my OpenVPN on pFSense setup tutorial on these links:
Server part: https://www.informaticar.net/how-to-setup-openvpn-on-pfsense/
Client part: https://www.informaticar.net/how-to-setup-openvpn-pfsense-version-on-client-pc/
After you finish that tutorial you`ll be able to connect to the VPN, but probably will not be able to access LAN resources.
Solution is simple – but for some reason it will not work for me in initial OpenVPN setup. I have to edit OpenVPN configuration after setting up.
Here is the solution.
If you followed my pFSense OpenVPN tutorial then you have Firewall and NAT setup correctly.
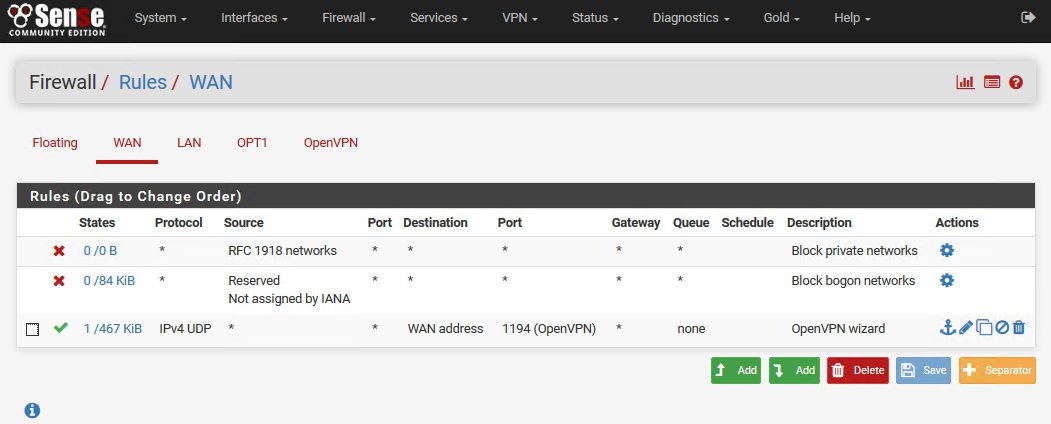
Firewall for WAN interface should look like this:
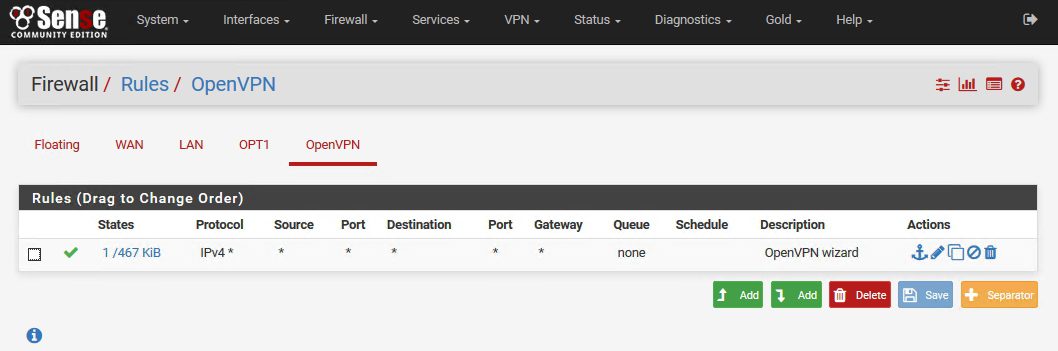
Under OpenVPN there should be also one firewall rule
That is it for the firewall – we don`t need custom rules for OpenVPN under LAN or OPT1 interface.
You can have your own custom LAN Firewall rules with disabled default “allow all” rules – it will work – you don`t need anything for the OpenVPN there.
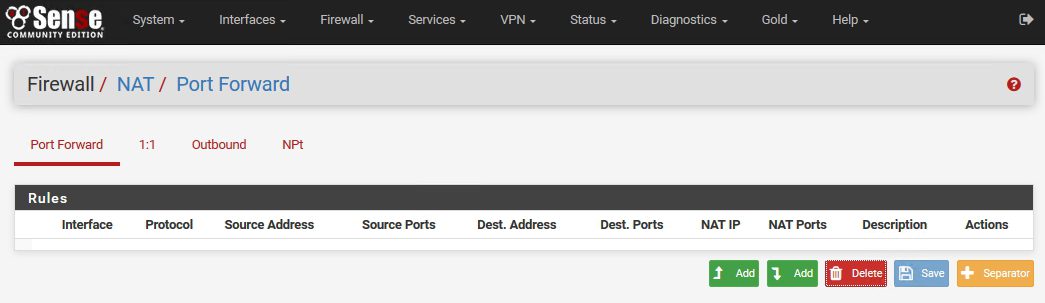
As for the NAT rules – for OpenVPN and simple default VPN setup you don`t need Port Forward settings.
Your Port Forward screen can look like this
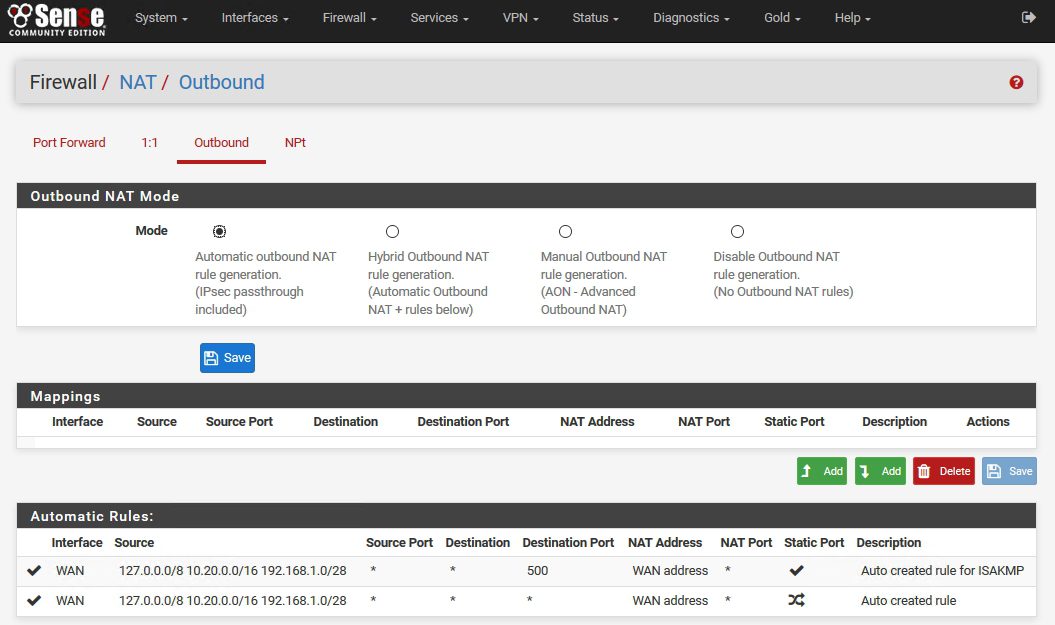
NAT Outbound Mode can be on Automatic Outbound NAT rule generation.
Why am I writing these details – because documentation around the web is full of different scenarios and tutorials – I combined a lot of stuff (mostly because I didn`t know pFSense interface and logic well) and my results were bad.
We will now setup access to the LAN resources over VPN connection
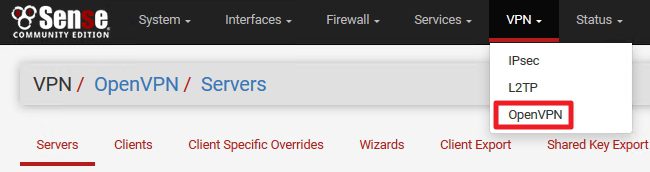
Log on to your pFSense webConfigurator
VPN | OpenVPN | Servers
Click on Edit
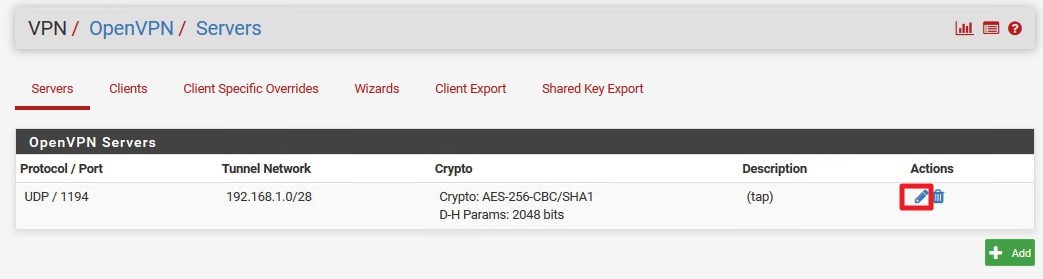
When Settings page of your OpenVPN server opens head to Tunnel Settings section first
Tunnel Settings | IPv4 Tunnel Network
As I already mentioned in article where is tutorial for VPN setup – Ipv4 Tunnel Network should be in a range different from your production network range. 192.168.xx.xx range is not a bad choice if you don`t have enormous number of VPN connections.
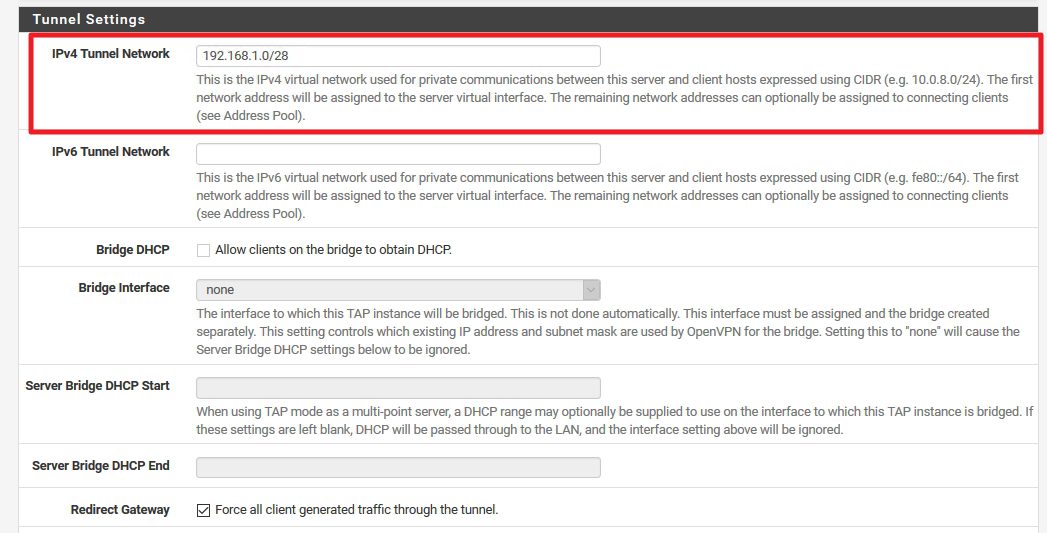
Next stop is under Advanced Configuration
Advanced Configuration | Custom options
10.20.20.0/16 is my production network. We need to push that route to the VPN settings
So subnet ID for my network is 10.20.0.0 and subnet mask is 16bit which means 255.255.0.0
You`ll enter here data of your production network – network on which computer to which you wish to access reside.
Command is
push “route 10.20.0.0 255.255.0.0”
Save
Let’s test our configuration.
On the host server I have configured RDP and Simple File Share
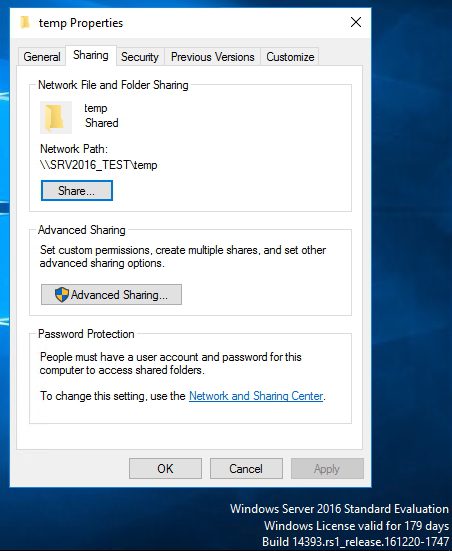
File Share
Make sure that you have file share exception configured in firewall on the machine you wish to access
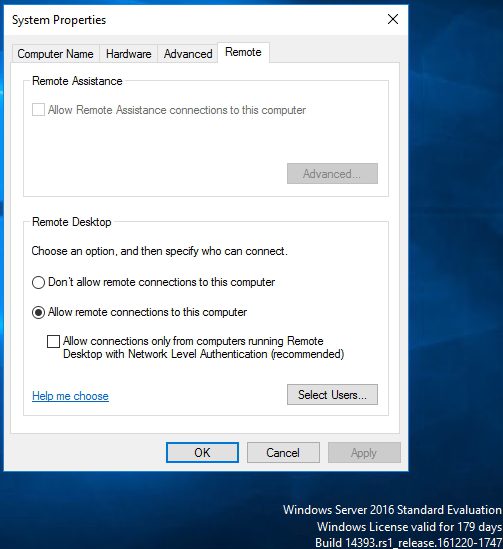
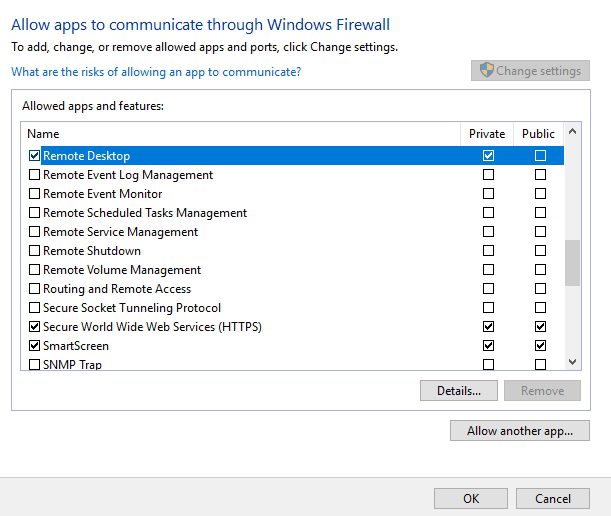
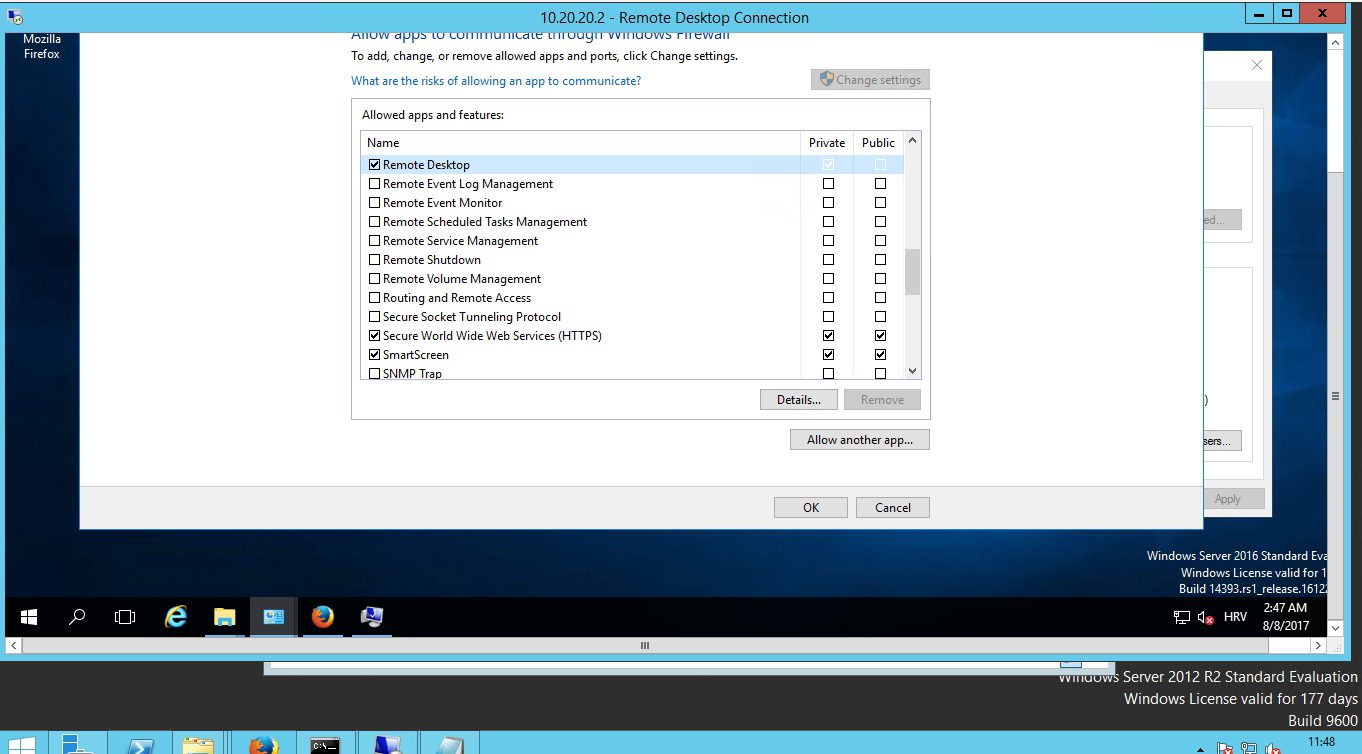
Remote Desktop
Also RDP needs to be allowed in the firewall
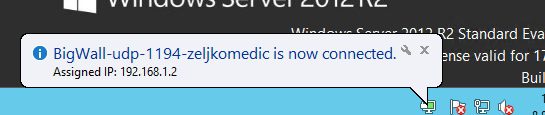
Now, to the guest server – connect to the VPN (maybe you`ll need to start OpenVPN with “Run As Administrator” rights – sometimes Windows won`t add route we defined to the table. So, to be sure, always start OpenVPN Client with Administrative rights
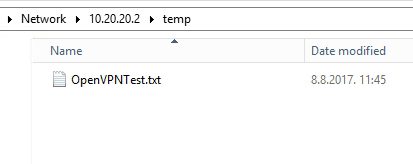
Now, let’s try access to the file share
Works – so we`ll add a document for a test – we`ll name it OpenVPNTest.txt
That is working – no errors – document is on the host server.
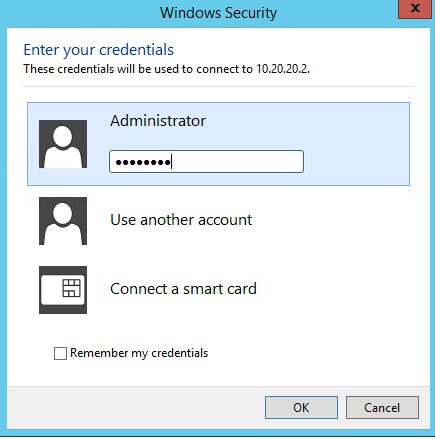
One more test – RDP connection
Success
Conclusion is that we now have fully functioning OpenVPN on pFSense. Once again, my recommendations for the pFSense – support project if you can.
pFSense article series:
How to install pFSense on Hyper-V – https://www.informaticar.net/how-to-install-pfsense-on-hyper-v/
How to configure pFSense – https://www.informaticar.net/how-to-configure-pfsense/
How to define firewall rules on pFSense – https://www.informaticar.net/how-to-define-firewall-rules-on-pfsense/
How to create port forwarding on pFSense – https://www.informaticar.net/create-port-forwarding-on-pfsense/
How to setup OpenVPN on pFSense – https://www.informaticar.net/how-to-setup-openvpn-on-pfsense/
How to setup OpenVPN on client (pFSense) – https://www.informaticar.net/how-to-setup-openvpn-pfsense-version-on-client-pc/
OpenVPN on pFSense: Enable access to the LAN resources – https://www.informaticar.net/openvpn-on-pfsense-enable-access-to-the-lan-resources/
How to revocate user certificate on pFSense – https://www.informaticar.net/how-to-revocate-user-certificate-on-pfsense-openvpn/
How to import PFX certificate to pFSense – https://www.informaticar.net/how-to-import-pfx-certificate-to-pfsense/